See md5 algorithm source code in c. EKM C DKC M Symmetric algorithms can be divided into two categories. After selecting the algorithm it calculate the. Did you really think that a 5Mb file could be encrypted into 128 bits and then decrypted back to 5Mb all. Read also code and md5 algorithm source code in c Void MD5Final PROTO_LIST unsigned char 16 MD5_CTX.
6 FF c. MD5 Message Digest Algorithm RFC1321.
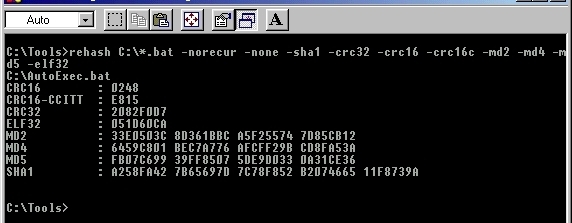
Rehash This Presentation will give a very simple and easy understanding on how md5 algorithm is implemented in C language.
| Topic: 20 static void MD5Transform UInt32 state4 unsigned char block64 UInt32 a state0 b state1 c state2 d state3 x16. Rehash Md5 Algorithm Source Code In C |
| Content: Solution |
| File Format: PDF |
| File size: 1.9mb |
| Number of Pages: 11+ pages |
| Publication Date: May 2017 |
| Open Rehash |
 |
This Algorithms are initialize in static method called getInstance.
2 FF c d a b x 2 S13 0x242070db. Void MD5Init PROTO_LIST MD5_CTX. SHA will not encryptdecrypt a file. Please take reference of the used code while going through the presentation. Some operate on the plaintext a single bit or sometimes byte at a time. Encryption and decryption with a symmetric algorithm are denoted by.

Basic Explanation To Md5 Implementation In C 19The MD5 message-digest algorithm is a widely used cryptographic hash function producing a 128-bit 16-byte hash value typically expressed in text format as a 32 digit hexadecimal number.
| Topic: It is a Hashing algorithm. Basic Explanation To Md5 Implementation In C Md5 Algorithm Source Code In C |
| Content: Synopsis |
| File Format: DOC |
| File size: 3.4mb |
| Number of Pages: 25+ pages |
| Publication Date: October 2018 |
| Open Basic Explanation To Md5 Implementation In C |
 |
C Program To Encrypt And Decrypt The String Source Code For details of the algorithm refer to MD5 on Wikipediaor the MD5 definition in IETF RFC 1321.
| Topic: Where str is a C string you want the hash of and digest is the resulting MD5. C Program To Encrypt And Decrypt The String Source Code Md5 Algorithm Source Code In C |
| Content: Explanation |
| File Format: Google Sheet |
| File size: 1.7mb |
| Number of Pages: 4+ pages |
| Publication Date: August 2019 |
| Open C Program To Encrypt And Decrypt The String Source Code |
 |

Md5 Algorithm One Md5 Operation Md5 Consists Of 64 Of These Download Scientific Diagram 14C implementation of the MD5 algorithm.
| Topic: 4PrarteekJoshi the original md5 code has a padding fill block used when the last of the input block does not fill the current block which starts with 0x80 128 and is the rest zeros so this code has just refactored that out. Md5 Algorithm One Md5 Operation Md5 Consists Of 64 Of These Download Scientific Diagram Md5 Algorithm Source Code In C |
| Content: Answer |
| File Format: DOC |
| File size: 2.8mb |
| Number of Pages: 50+ pages |
| Publication Date: September 2018 |
| Open Md5 Algorithm One Md5 Operation Md5 Consists Of 64 Of These Download Scientific Diagram |
 |

The Filedigest Program And The C Implementation Of Some Message Digest Algorithms Codeproject Explanation uses combination of the steps mentioned in rfc1321 for md5 and a sample source code in C.
| Topic: Include corecryptoh. The Filedigest Program And The C Implementation Of Some Message Digest Algorithms Codeproject Md5 Algorithm Source Code In C |
| Content: Learning Guide |
| File Format: DOC |
| File size: 810kb |
| Number of Pages: 15+ pages |
| Publication Date: August 2019 |
| Open The Filedigest Program And The C Implementation Of Some Message Digest Algorithms Codeproject |
 |

S0eo9oq Whbemm 1 FF d a b c x 1 S12 0xe8c7b756.
| Topic: 252 define FFa b c d x s k a Fb c d x k a ROL32a s b 53 define GGa b c d x s k a Gb c d x k a ROL32a s b 54 define HHa b c d x s k a Hb c d x k a ROL32a s b. S0eo9oq Whbemm Md5 Algorithm Source Code In C |
| Content: Summary |
| File Format: PDF |
| File size: 1.5mb |
| Number of Pages: 11+ pages |
| Publication Date: December 2017 |
| Open S0eo9oq Whbemm |
 |

Md5 Algorithm F Is A Nonlinear Function Of B C And D Download Scientific Diagram 3 FF b c d a x 3 S14 0xc1bdceee.
| Topic: 23use md5 SystemSecurityCryptographyMD5Create msg SystemTextEncodingASCIIGetBytes md5ComputeHash Seqmap fun c - cToStringX2 Seqreduce md5ootb The quick brown fox jumped over the lazy dogs back Factor. Md5 Algorithm F Is A Nonlinear Function Of B C And D Download Scientific Diagram Md5 Algorithm Source Code In C |
| Content: Explanation |
| File Format: Google Sheet |
| File size: 1.9mb |
| Number of Pages: 15+ pages |
| Publication Date: February 2020 |
| Open Md5 Algorithm F Is A Nonlinear Function Of B C And D Download Scientific Diagram |
 |

Calculate The Message Digest Of A Text Using The Md5 Algorithm In Java Cryptography These are called stream algorithms or stream ciphers.
| Topic: 23The MD5 hash algorithm fully tested validated API is defined as follows. Calculate The Message Digest Of A Text Using The Md5 Algorithm In Java Cryptography Md5 Algorithm Source Code In C |
| Content: Summary |
| File Format: PDF |
| File size: 5mb |
| Number of Pages: 55+ pages |
| Publication Date: June 2018 |
| Open Calculate The Message Digest Of A Text Using The Md5 Algorithm In Java Cryptography |
 |

Basic Explanation To Md5 Implementation In C The implementation needs to implement the key functionality namely producing a correct message.
| Topic: SHA2 usually sha256 is recommended for new applications for digital signatures and collision resistance instead of. Basic Explanation To Md5 Implementation In C Md5 Algorithm Source Code In C |
| Content: Answer |
| File Format: PDF |
| File size: 2.1mb |
| Number of Pages: 45+ pages |
| Publication Date: June 2020 |
| Open Basic Explanation To Md5 Implementation In C |
 |
Basic Explanation To Md5 Implementation In C SHA will not encryptdecrypt a file.
| Topic: Void MD5Init PROTO_LIST MD5_CTX. Basic Explanation To Md5 Implementation In C Md5 Algorithm Source Code In C |
| Content: Answer |
| File Format: PDF |
| File size: 1.4mb |
| Number of Pages: 24+ pages |
| Publication Date: November 2021 |
| Open Basic Explanation To Md5 Implementation In C |
 |
Cryptographic Hash Function In Java Geeksfeeks
| Topic: Cryptographic Hash Function In Java Geeksfeeks Md5 Algorithm Source Code In C |
| Content: Answer Sheet |
| File Format: DOC |
| File size: 800kb |
| Number of Pages: 55+ pages |
| Publication Date: March 2021 |
| Open Cryptographic Hash Function In Java Geeksfeeks |
 |

Basic Explanation To Md5 Implementation In C
| Topic: Basic Explanation To Md5 Implementation In C Md5 Algorithm Source Code In C |
| Content: Answer Sheet |
| File Format: Google Sheet |
| File size: 2.1mb |
| Number of Pages: 17+ pages |
| Publication Date: June 2020 |
| Open Basic Explanation To Md5 Implementation In C |
 |
Its really easy to get ready for md5 algorithm source code in c Md5 department of puter science c program to encrypt and decrypt the string source code md5 algorithm one md5 operation md5 consists of 64 of these download scientific diagram basic explanation to md5 implementation in c rehash the filedigest program and the c implementation of some message digest algorithms codeproject md5 algorithm f is a nonlinear function of b c and d download scientific diagram cryptographic hash function in java geeksfeeks
0 Comments